Learning Path/NMAP Documentation and Commands
From Wiki Aghanim
Jump to navigationJump to search
This is my notes from the Junior Pentesting course at TryHackMe. This course takes you through the basics and some advanced topics regarding penetration testing.
NMAP Live Host Discovery
| Scan Type | Example Command |
| ARP Scan | sudo nmap -PR -sn MACHINE_IP/24 |
| ICMP Echo Scan | sudo nmap -PE -sn MACHINE_IP/24 |
| ICMP Timestamp Scan | sudo nmap -PP -sn MACHINE_IP/24 |
| ICMP Address Mask Scan | sudo nmap -PM -sn MACHINE_IP/24 |
| TCP SYN Ping Scan | sudo nmap -PS22,80,443 -sn MACHINE_IP/30 |
| TCP ACK Ping Scan | sudo nmap -PA22,80,443 -sn MACHINE_IP/30 |
| UDP Ping Scan | sudo nmap -PU53,161,162 -sn MACHINE_IP/30 |
Remember to add -sn if you are only interested in host discovery without port-scanning. Omitting -sn will let Nmap default to port-scanning the live hosts.
| Option | Purpose |
| -n | no DNS lookup |
| -R | reverse-DNS lookup for all hosts |
| -sn | host discovery only |
NMAP Basic Port Scans
- Open: indicates that a service is listening on the specified port.* Closed: indicates that no service is listening on the specified port, although the port is accessible. By accessible, we mean that it is reachable and is not blocked by a firewall or other security appliances/programs.* Filtered: means that Nmap cannot determine if the port is open or closed because the port is not accessible. This state is usually due to a firewall preventing Nmap from reaching that port. Nmap’s packets may be blocked from reaching the port; alternatively, the responses are blocked from reaching Nmap’s host.* Unfiltered: means that Nmap cannot determine if the port is open or closed, although the port is accessible. This state is encountered when using an ACK scan -sA.* Open|Filtered: This means that Nmap cannot determine whether the port is open or filtered.* Closed|Filtered: This means that Nmap cannot decide whether a port is closed or filtered.
TCP Flags
- URG: Urgent flag indicates that the urgent pointer filed is significant. The urgent pointer indicates that the incoming data is urgent, and that a TCP segment with the URG flag set is processed immediately without consideration of having to wait on previously sent TCP segments.* ACK: Acknowledgement flag indicates that the acknowledgement number is significant. It is used to acknowledge the receipt of a TCP segment.* PSH: Push flag asking TCP to pass the data to the application promptly.* RST: Reset flag is used to reset the connection. Another device, such as a firewall, might send it to tear a TCP connection. This flag is also used when data is sent to a host and there is no service on the receiving end to answer.* SYN: Synchronize flag is used to initiate a TCP 3-way handshake and synchronize sequence numbers with the other host. The sequence number should be set randomly during TCP connection establishment.* FIN: The sender has no more data to send.
Timings
| Timings | Description |
| T0 | paranoid (0) |
| T1 | sneaky (1) |
| T2 | polite (2) |
| T3 | normal (3) |
| T4 | aggressive (4) |
| T5 | insane (5) |
Summary
| Port Scan Type | Example Command |
| TCP Connect Scan | nmap -sT MACHINE_IP |
| TCP SYN Scan | sudo nmap -sS MACHINE_IP |
| UDP Scan | sudo nmap -sU MACHINE_IP |
These scan types should get you started discovering running TCP and UDP services on a target host.
| Option | Purpose |
| -p- | all ports |
| -p1-1023 | scan ports 1 to 1023 |
| -F | 100 most common ports |
| -r | scan ports in consecutive order |
| -T<0-5> | -T0 being the slowest and T5 the fastest |
| --max-rate 50 | rate <= 50 packets/sec |
| --min-rate 15 | rate >= 15 packets/sec |
| --min-parallelism 100 | at least 100 probes in parallel |
NMAP Advanced Port Scans
| Port Scan Type | Example Command |
| TCP Null Scan | sudo nmap -sN MACHINE_IP |
| TCP FIN Scan | sudo nmap -sF MACHINE_IP |
| TCP Xmas Scan | sudo nmap -sX MACHINE_IP |
| TCP Maimon Scan | sudo nmap -sM MACHINE_IP |
| TCP ACK Scan | sudo nmap -sA MACHINE_IP |
| TCP Window Scan | sudo nmap -sW MACHINE_IP |
| Custom TCP Scan | sudo nmap --scanflags URGACKPSHRSTSYNFIN MACHINE_IP |
| Spoofed Source IP | sudo nmap -S SPOOFED_IP MACHINE_IP |
| Spoofed MAC Address | --spoof-mac SPOOFED_MAC |
| Decoy Scan | nmap -D DECOY_IP,ME MACHINE_IP |
| Idle (Zombie) Scan | sudo nmap -sI ZOMBIE_IP MACHINE_IP |
| Fragment IP data into 8 bytes | -f |
| Fragment IP data into 16 bytes | -ff |
| Option | Purpose |
| --source-port PORT_NUM | specify source port number |
| --data-length NUM | append random data to reach given length |
These scan types rely on setting TCP flags in unexpected ways to prompt ports for a reply. Null, FIN, and Xmas scan provoke a response from closed ports, while Maimon, ACK, and Window scans provoke a response from open and closed ports.
| Option | Purpose |
| --reason | explains how Nmap made its conclusion |
| -v | verbose |
| -vv | very verbose |
| -d | debugging |
| -dd | more details for debugging |
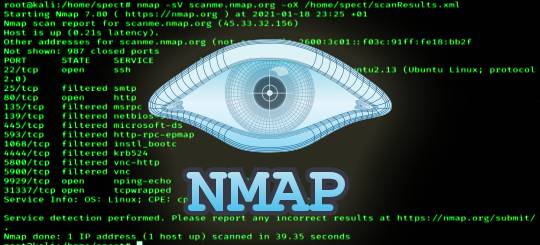
NMAP Post Port Scans
| Option | Meaning |
| -sV | determine service/version info on open ports |
| -sV --version-light | try the most likely probes (2) |
| -sV --version-all | try all available probes (9) |
| -O | detect OS |
| --traceroute | run traceroute to target |
| --script=SCRIPTS | Nmap scripts to run |
| -sC or --script=default | run default scripts |
| -A | equivalent to -sV -O -sC --traceroute |
| -oN | save output in normal format |
| -oG | save output in grepable format |
| -oX | save output in XML format |
| -oA | save output in normal, XML and Grepable formats |